The SEC Cybersecurity Disclosure Rule Is Official: The Path to Compliance Starts Now
After much anticipation, the new SEC cybersecurity reporting rule is in the books. Companies should begin preparing now to ensure reporting readiness by the end of the year.
On Wednesday, the US Securities and Exchange Commission (SEC) released its final rule on cybersecurity reporting. Adopted by a three-to-two vote, the new requirements aim to enhance and standardize disclosures regarding cybersecurity risk management, strategy, governance, and how public companies report cybersecurity incidents. The official rule reflects several updates based on feedback received during the comment period. All registrants must provide disclosures beginning with annual reports for fiscal years ending on or after Dec. 15, 2023.
Three key takeaways from the final rule
The newly adopted SEC cybersecurity rule addresses three key areas of disclosure:
- Risk, management, and strategy. Within the 10-K, companies will need to describe processes, if any, for the assessment, identification, and management of material risks from cybersecurity threats and describe whether any risks from cybersecurity threats have materially affected or are reasonably likely to materially affect business strategy, results of operations, or financial condition.
- Governance. Disclosures in the 10-K must include descriptions of the board’s oversight of cybersecurity risks and management’s role in assessing and managing material risks from cybersecurity threats.
- Material cybersecurity incident. Companies must disclose in an 8-K filing any cybersecurity incident that is determined to be material and describe the material aspects of the incident’s nature, scope, timing, and impact (or reasonably likely impact.) The required 8-K filing must be filed within four business days of determining an incident’s materiality. There is an exception if the US Attorney General determines immediate disclosure would pose a substantial risk to national security or public safety. Any information that is not determined or not available at the time of the initial 8-K filing must be disclosed via required amendments.
For each of these areas, the rule also addresses related forms for Foreign Private Issuers.
Important changes to note
The SEC adopted several changes to its proposed rule in response to comments and discussions during the rule adoption proceedings. Changes to the final rule include:
- Narrowing the required information reported following a material cybersecurity incident and reinforcing that technical details are not required.
- Providing disclosure delay options for national security or public safety as considered by the Attorney General.
- Removing the requirement for specific cybersecurity board expertise.
These updates signal that the SEC heard companies’ concerns shared in comments and made several adjustments to reporting requirements.
Preparing for compliance
While the first reporting of new disclosures won’t be seen until December, companies should begin early to be fully prepared to comply with this new rule. Here are five actions to get started:
- Conduct a compliance diagnostic. Cybersecurity management is certainly not a new topic. Companies can start by understanding and evaluating where their current cybersecurity practices stand in comparison to the new SEC requirements. Make a list of where improvements are needed to bring the companies’ practices in line.
- Revisit cybersecurity processes. Now is a good time to fully review and address issues related to cybersecurity systems, including policies and procedures. If material risks are not clearly identified and addressed within the current system, consider adding this element as it will drive how the company determines the materiality of future incidents for reporting.
- Create a “practice” response. Have the cybersecurity team prepare responses using the company’s current cybersecurity state. This exercise may help management more clearly identify areas where changes may need to be made to improve compliance.
- Prepare an incident response plan. While many companies already have a plan in place to respond to cybersecurity incidents, most will need to update the plan and add a new step for determining the materiality of an incident. Organizations may also need to reconsider who needs to be drawn into the conversation when an incident occurs. Making these types of additions to a response plan can change the communication dynamic and how the board oversight is engaged. It’s a good idea to run through an incident reporting simulation to ensure the company has a well-thought-out approach to determining the materiality of potential incidents, communicating material incidents via the 8-K, and identifying the need for ongoing update communications with the SEC. The response plan should include a “break-the-glass” reference outlining roles and responsibilities in advance, which will drive a more coordinated response should an incident arise.
- Align with ESG Companies that release sustainability reports or include ESG information on their websites will want to update these communications with their new cybersecurity disclosures. Companies should always maintain consistent ESG reporting across disclosures, aligning the 8-K, 10-K, and CSR wherever possible. While the disclosure of incidents can be reserved for the 8-K, references to the cybersecurity management structure should be included across all communications to help avoid any discrepancies between financial disclosures and sustainability reporting that could draw scrutiny and questioning from the SEC.
Consider following the leaders
The SEC recognizes that many companies are already doing a good job of disclosing cybersecurity management. Companies that need a little inspiration for preparing their own disclosures may want to check out a few strong reporting examples:
- In its 10-K as a large, accelerated filer, Intuit covers a variety of cybersecurity risks in the Operations Risk section of the filing.
- Commercial banking organization Northern Trust offers an effective model for cybersecurity governance disclosure, presenting the following diagram that illustrates the company’s cybersecurity oversight.
Figure: Example cybersecurity governance disclosure
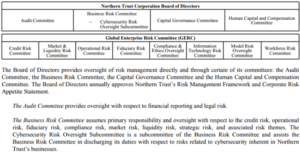
Source: Northern Trust

